AML vs KYC: Key differences and compliance essentials

AML and KYC are regulatory frameworks designed to prevent financial crime. KYC (Know Your Customer) verifies a customer’s identity during customer onboarding, while AML (Anti-Money Laundering) focuses on monitoring, detecting, and reporting suspicious activity over time. Together, AML and KYC help organizations reduce fraud, comply with regulations, and manage financial risk.
| KYC (Know Your Customer) | AML (Anti-Money Laundering) | |
| Goal | Verify customer identity and evaluate customer risk | Prevent, identify, and report money laundering and other financial crime |
| When it occurs | Customer onboarding and transaction monitoring | Ongoing monitoring throughout the customer lifecycle |
| Key activities | Customer identification, verification, and due diligence | Customer behavior monitoring, internal compliance reviews, audit trail creation, and suspicious activity reporting |
| Outputs | Verified customer risk profiles and due diligence monitoring levels | Compliance programs, fraud alerts, and SARs backed by audit trails |
Quick takeaway: KYC is usually a component of an AML program—KYC establishes who the customer is, and AML governs how you monitor and respond over time.
Modern AML KYC programs rely on accurate customer data. Smarty provides APIs for address validation, enrichment, and property data that organizations need to strengthen identity verification, reduce risk, and support compliance workflows.
In this article, we’ll get to know the dynamic duo of AML and KYC:
- What is AML/KYC?
- AML vs KYC: what’s the difference?
- How AML and KYC work together
- The 5 stages of KYC
- The 3 stages of AML
- AML checklist and compliance checklist
- Who needs to comply with KYC AML?
- Tools and solutions that support AML/KYC programs
- TL;DR
What is AML/KYC?
AML/KYC, also referred to as AML KYC, is the shorthand term for two regulatory compliance frameworks designed to prevent financial crime: Anti-Money Laundering (AML) and Know Your Customer (KYC).
AML includes several regulatory processes that financial institutions follow to monitor, detect, and report money laundering or other financial crimes.
KYC is a regulatory process that focuses on verifying customer identities and evaluating the risk they pose to a company.
These regulatory compliance frameworks are often paired because they help finance companies—including banks, credit unions, fintechs, payments companies, crypto exchanges, insurance providers, and real estate services—limit fraud, boost compliance, safeguard customers’ assets, and mitigate risk.
AML vs KYC: what’s the difference?
AML and KYC work together to prevent financial crime, but they have distinct differences. KYC is a process for verifying customer identities. It’s a part of AML, an umbrella term for several processes that help finance companies monitor customer activities, flag suspicious behavior, and report fraud.
Don’t worry, though; these differences are exactly what make this dynamic duo stronger.
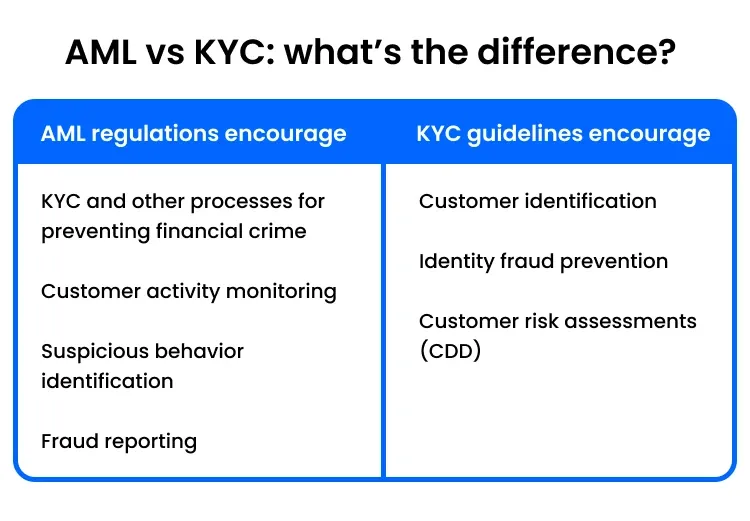
Purpose of KYC
KYC helps prevent financial crime by verifying who a customer is and assessing their risk during onboarding. That lets you catch fraud early in the onboarding process, long before it leads to chargebacks, investigations, or regulatory trouble.
When you verify a customer’s identity up front, you limit fraud and identity theft by blocking accounts created with fake or stolen information. That means fewer investigations, fewer potential fines, and less damage to your reputation.
KYC processes also include customer due diligence (CDD)—a risk assessment based on customer information like occupation, source of funds, and expected transaction patterns. These details power ongoing monitoring, helping financial institutions flag suspicious activity, prevent financial crime, and comply with AML regulations.
Purpose of AML
AML is an umbrella term for several standards that work together to fight financial crime, including KYC. AML’s goal is to prevent money laundering throughout the customer lifecycle by continuously monitoring customer activity, identifying suspicious behavior, and reporting potential fraud cases.
By complying with AML regulations, financial institutions can better manage financial risk and prevent significant losses from AML fines.
How AML and KYC work together
AML and KYC really start to jive when they both rely on accurate data. If one relies on bad data, the other suffers too. And if that bad data happens to be bad address data, things can get really messy, really fast.
If your company isn’t regularly checking your address database for accuracy, outdated records, or duplicate entries, you could have bad address data waiting to turn your AML KYC efforts into a full-blown mess-terpiece (see what we did there?)
Address validation will compare your addresses against an authoritative database to determine whether they’re real and valid, making you better equipped to manage customer data.
Plus, validated addresses come with metadata, making it even easier to spot fraudulent addresses. These data points include:
- Residential Delivery Indicator (RDI), which categorizes a building as zoned for residential or commercial use.
- Vacancy status, an indicator for whether an address is currently vacant or occupied.
These hyper-accurate data points (and 53 more!) help AML KYC solutions better identify fraudulent addresses during the application process and flag suspicious changes to a customer’s address.
The 5 stages of KYC
Now that we’ve covered what KYC is and how it differs from AML, let’s dive deeper. Here’s how KYC works in just 5 stages.

1. Customer identification
KYC starts by identifying a customer, often through customer identification programs (CIPs).
Before an individual can open an account, CIPs collect customers’:
- Name
- Date of birth
- Address
- Government-issued identity documents
- Contact info
If the customer is a business, they must provide their:
- Legal business name
- Address
- Entity type
- Tax ID or registration number
- Country of incorporation
- Owners’ and controllers’ names
2. Identity verification
Finance companies verify a customer’s identity by checking their details against government records or by running background checks.
If everything lines up, financial institutions move forward with a reasonable belief that they know the customer’s identity.
Otherwise, they decline, restrict, or close the account. And if it smells fishy, they file a Suspicious Activities Report (SAR) to stay KYC-compliant.
3. Risk assessment
After a customer’s identity has been verified, financial institutions evaluate the financial risk the customer poses. Several types of risk are considered, including:
- Customer risk: Is the customer an individual or an entity? What is the customer’s occupation? Is the customer in a high-risk role? Are they considered politically exposed persons?
- Geographic risk: Where is the customer located? Does that location have a high corruption risk?
- Transactional risk: What type of transactions is this customer likely to complete?
4. Due diligence (CDD/EDD)
After assessing the risk profile tied to a potential or current customer, CDD procedures take the driver’s seat. Finance companies evaluate the level of risk a customer poses, then create a plan for ongoing monitoring.
If suspicious activity is flagged during this monitoring, enhanced due diligence (EDD) steals the spotlight.
EDD mandates an investigation into a suspicious customer profile to determine the customer’s source of funds and wealth, and review their transactions and documentation.
5. Ongoing monitoring
After completing the first four KYC stages, financial institutions continue to monitor a customer's transactions until account closure. In practice, this involves automated real-time or daily checks so that whenever fraud appears, they’re ready to get after it.
The depth of this transaction monitoring should be risk-based. For customers with low risk scores, automated transaction checks and flagged transactions may be enough. Ongoing monitoring of customers with higher risk scores, like politically exposed persons, will require a regularly established source of wealth and funds.
In both instances, it’s important to document any monitoring and keep those records up to date. Even after a customer closes their account, these records should be kept for at least five years.
In short, KYC happens in five stages:
- Customer identification: Collect a customer’s identifying information.
- Identity verification: Validate a customer’s identity using their identifying information and authoritative databases.
- Risk assessment: Evaluate the financial risk the customer poses to your company.
- Due diligence (CDD/EDD): Plan how to monitor a customer’s risk long-term.
- Ongoing monitoring: Utilize AML processes to continuously monitor a customer’s transactions.
The 3 stages of AML
The United Nations Office on Drugs and Crime reported that globally, $800 billion to $2 trillion is laundered in one year. According to the FBI, $300 billion is laundered in the US alone. AML strives to prevent finance companies from adding to that number through these 3 stages.
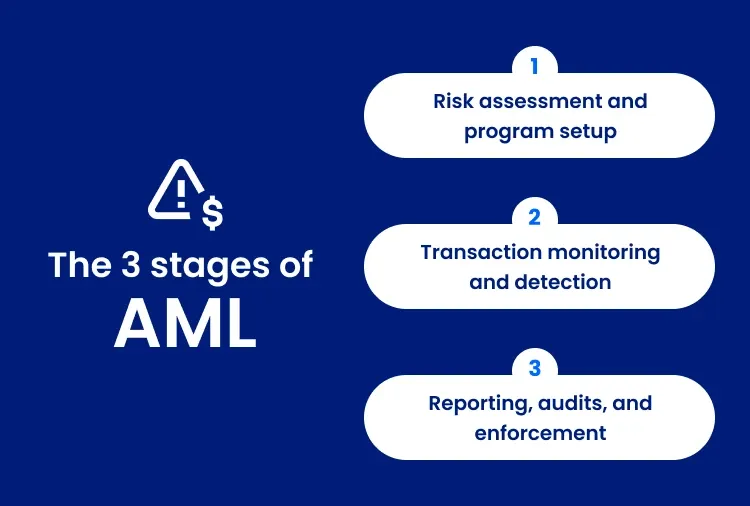
1. Risk assessment and program setup
To create a strong AML program, financial institutions need to understand their financial risk through a risk assessment.
From there, they can set up internal systems to test for compliance and train the folks overseeing day-to-day compliance.
2. Transaction monitoring and detection
With a program in place, financial institutions can then monitor transactions and detect any eyebrow-raising activity. This ongoing monitoring can identify account takeovers by flagging suspicious changes to phone numbers, emails, or even addresses.
3. Reporting, audits, and enforcement
Address verification catches unusual patterns or sudden changes in customer addresses, so you can quickly submit AML KYC compliance reviews. For Suspicious Activity Reports (SAR), which must be filed within 30 days of detection, this boost in speed helps financial institutions stay compliant.
To recap, the three stages of AML are:
- Risk assessment and program setup: Set up internal systems to ensure long-term compliance, and train folks to oversee day-to-day compliance.
- Transaction monitoring and detection: Monitor financial transactions to detect unusual activity, such as sudden changes to phone numbers, emails, or addresses.
- Reporting, audits, and enforcement: When you suspect fraud, file Suspicious Activity Reports (SARs) within 30 days of detection, and keep clear records for any audits.
AML checklist and compliance checklist
So, you get AML and why it’s a big deal. Neat. Now it’s time to put it into practice and implement your own AML solution. Let’s get you on your way.
AML checklist example for building and maintaining a program
This step-by-step Anti-Money Laundering compliance checklist for compliance officers is a roadmap for building and maintaining an AML program. It starts with mandatory AML policies, like CDD and KYC procedures, and continues through ongoing customer monitoring and fraud reporting.
- Implement a Know Your Customer (KYC) process to verify customer identities and addresses at onboarding
- Conduct customer due diligence (CDD) to assess the risk a customer poses
- Apply enhanced due diligence (EDD) for high-risk customers
- Maintain internal AML policies to identify, measure, monitor, and control financial crime risk
- Designate and train personnel to ensure day-to-day AML compliance
- Use quality controls, IT sources, and systems to support AML
- Monitor customer transactions
- Continuously verify customer addresses to catch suspicious address changes
- Maintain audit trails
- File Suspicious Activity Reports (SARs) as needed
Documentation management Anti-Money Laundering compliance checklist:
For document managers, financial clerks, auditors, and compliance officers, this Anti-Money Laundering compliance checklist template provides an operational and audit-focused approach to Anti-Money Laundering compliance.
- Keep CDD and EDD risk profiling records
- Document transactions monitoring
- File justification for SARs with audit trails
- Regularly test and review internal AML processes and policies
- Run employee AML trainings
Who needs to comply with KYC AML?
KYC AML solutions aren’t just a concern for banks. Money Services Businesses like credit unions, fintechs, payments companies, real estate services, insurance providers, and crypto exchanges also have a horse in the race. Here’s why.

Banks and credit unions
In the US, the Bank Secrecy Act (BSA) has combated money laundering since 1970. AML is a vital part of BSA compliance that helps banks and credit unions monitor how well their procedures meet legal requirements.
Fintech and payments companies
Like banks, Money Services Businesses (MSBs), fintechs, and payment companies handle transactions. To prevent financial crimes, they need KYC AML solutions to detect and report suspicious activity.
Crypto exchanges
Crypto exchanges are considered MSBs by the US Financial Crimes Enforcement Network, so they’re also required to comply with KYC AML and SAR filing requirements.
Insurance providers
Certain insurance products can be used to facilitate money laundering. To mitigate this risk, insurers offering life insurance policies, annuity contracts, or any product with cash value features need an AML process in place.
Real estate and property services
Entities and trusts can disguise financial fraud through “all-cash” real estate sales. With AML processes, real estate and property services can keep bad actors from slipping through the cracks.
Tools and solutions that support AML/KYC programs
AML KYC can seem intimidating, but with top-notch address data solutions, you can spend less time worrying about fraudulent addresses slipping through the cracks and more time on the high-risk cases that need your attention the most.
Identity verification tools
AML KYC solutions start with identity verification. Unfortunately, fraudsters know this and love targeting platforms with weak KYC programs that ask for very basic information during signup.
If your platform doesn’t verify addresses after the application process, bad actors can waltz right in with a valid address, then change it to a fake one to avoid detection later.
By consistently verifying your customers’ addresses, you can shut down fraudsters who change their addresses to invalid ones after they apply, preventing much bigger problems down the road.
Address verification and enrichment
Like AML and KYC, address verification and enrichment are a dream team.
Using just two metadata points returned with address verification–Residential Delivery Indicators and vacancy status–you can flag suspicious properties.
Then, using rooftop-level geocodes—a pair of latitude and longitude coordinates that identify a specific place—you can compare a provided address with the exact location of the device used to create an account to further detect fraud.
Address enrichment adds even more detail to your address data so your records stay pristine. Plus, if you ever need it, you’ll have an audit trail that lines up with AML KYC compliance guidelines.
Risk scoring and monitoring platforms
Risk scores are only as accurate as the data used to create them. Up-to-date address data boosts risk-score accuracy with better risk screening, change monitoring, and real-time alerts.
Monitoring platforms, on the other hand, help you create an audit trail backed by evidence to show how you’ve detected any suspicious activity. These trails become quality SARs and keep your company AML/KYC compliant.
TL;DR
We get it. You’ve got so much going on, your to-do list has a to-do list. We’ll keep this simple and get you the facts you need. Here’s the rundown.
Anti-Money Laundering (AML) and Know Your Customer (KYC) are complementary compliance frameworks that work together to prevent financial crime. KYC establishes who a customer is, then AML steps up to bat to ensure their activity remains legitimate over time.
Strong AML KYC compliance programs depend on accurate customer data, continuous monitoring, and reliable verification tools. Smarty helps keep your address data up to date so you can catch bad addresses before they cause compliance trouble.

